
비야레알의 윙어인 사무엘 추쿠에제, 그는 이번 여름 이적시장에서 비야레알을 떠날 확률이 높게 평가되고 있었고 토트넘, 레알마드리드 등 여러 구단이 그의 영입에 큰 관심을 가지고 있었다.
토트넘의 경우 윙어 보강을 위해 비야레알로 임대 이적을 경험한 로 셀소와 추쿠에제의 스왑딜을 계획하기도 하였고 레알마드리드는 비니시우스의 백업 선수로 추쿠에제를 고려하고 있다는 소식까지 전해지고 있었다.
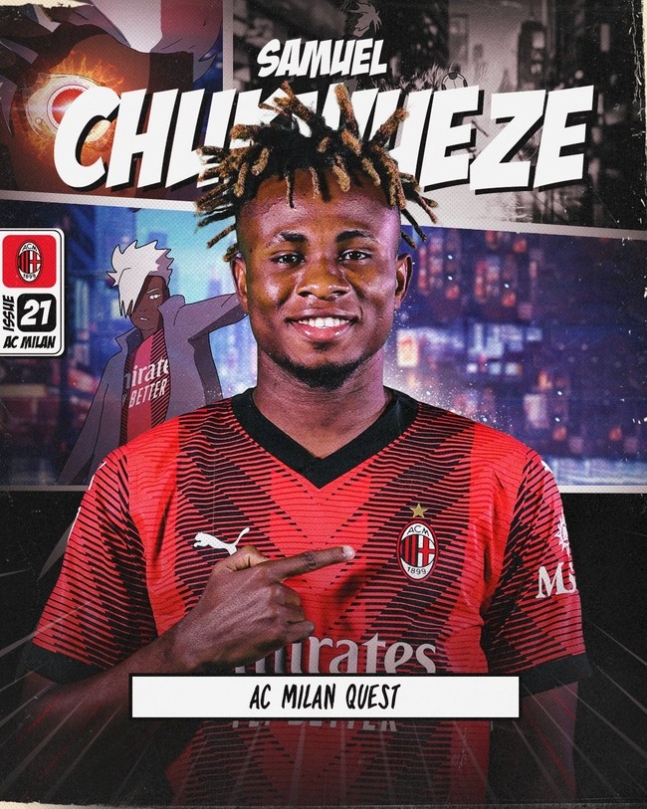
추쿠에제는 비야레알에게 이적료를 안길 것으로 예상되었던 가운데 그는 토트넘도 레알마드리드도 아닌 AC밀란 이적을 선택하며 세리에 진출을 알렸다.
AC밀란 홈페이지에서 "추쿠에제와 5년 계약을 체결했다"라고 발표했고 기본 이적료 281억+ 추가 옵션 112억이 포함된 총 393억의 이적료로 알려지고 있었다.
노란 잠수함을 떠나 AC밀란으로 향한 추쿠에제였으며 추쿠에제는 비야레알에서 5년을 보낸 뒤 새로운 커리어를 선택하게 되었다.
추쿠에제는 라리가에서 빠르고 유연한 드리블 실력을 보여주며 빅클럽들의 눈길을 사로잡은 가운데 AC밀란은 왼쪽에서 하파엘 레앙을 배치하고 오른쪽에 수준급 윙어를 배치하길 원하고 있었다.
AC밀란은 이전 주전 선수인 산드로 토날리를 뉴캐슬에 900억 이상에 금액으로 판매해 많은 비난을 받았지만 많은 이적료를 얻은 이들은 새로운 윙어를 영입하며 AC밀란 팬들을 환호하게 만들었다.
AC밀란 팬들은 추쿠에제 합류에 기뻐하고 있었다. 왼발잡이의 오른쪽 윙어는 쉽게 찾아볼 수 없었으며 오랜 기간 약점으로 지목받았던 오른쪽 측면이 추쿠에제로 제대로 보강되었다.
AC밀란은 양 측 날개를 레앙과 추쿠에제 듀오로 꾸릴 수 있게 되었으며 23-24시즌 세리에의 황금 날개 조합이 탄생할 수도 있었다.
추쿠에제가 22-23시즌 50경기 13골 11도움을 기록했다는 면에서 AC밀란의 활약은 더욱 큰 기대를 받고 있는 가운데 추쿠에제가 어떠한 활약을 보여줄 지 지켜봐야 했다.